"Old hackers never die. They just go to bitnet."
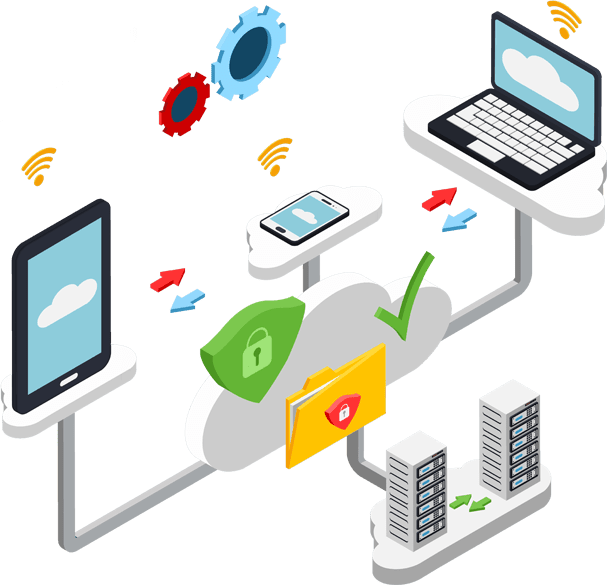
Cyber Secuirty Services
We provide air proof security services to your network, servers, cloud, application and application data flow . Following are our main services .
Security analysis

Our security analyst is responsible for maintaining the security and integrity of your data. Our main job is to analyze the security measures of a company and determine how effective they are
Ethical Hacking

A Certified Ethical Hacker is a skilled professional who understands and knows how to look for weaknesses and vulnerabilities in target systems and uses the same knowledge and tools as a malicious hacker, but in a lawful and legitimate manner to assess the security posture of a target system(s).
Threat Intelligence Analysis

We help organizations to identify and mitigate business risks by converting unknown internal and external threats into known threats.
Disaster Recovery

We will conduct business impact analysis, assessing risks, developing policies and procedures, and implementing a plan to recover your enterprise from disasters .
Penetration Testing

Our experts will do a penetration test, colloquially known as a pen test, pentest or ethical hacking, is an authorized simulated cyber attack on a computer system, performed to evaluate the security of the system.
Incident Handling

Our experts help organizations need to effectively handle post breach consequences by reducing the impact of the incident, from both a financial and reputational perspective.
Computer Forensic Investigator

Computer hacking forensic investigation is the process of detecting hacking attacks and properly extracting evidence to report the crime and conduct audits to prevent future attacks. Computer crime in today’s cyber world is on the rise. Computer Investigation techniques are being used by police, government and corporate entities globally .
Encryption Specialist

Our experts will help to make private encryptions for your applications.Our experts are well aware of current standards and industry algorithms like symmetric key cryptography like Feistel Networks, DES, and AES.
- Blowfish, Twofish, and Skipjack.
- Hashing algorithms including MD5, MD6, SHA, Gost, RIPMD 256 and others.
- Asymmetric cryptography including thorough descriptions of RSA, Elgamal, Elliptic Curve, and DSA.
- Significant concepts such as diffusion, confusion, and Kerkchoff’s principle.
- Also we help
- How to set up a VPN
- Encrypt a drive , steganography
Application Security

Application Security : we help you to produce secure applications with greater stability and fewer security risks to the consumer, therefore, making security a foremost thought. We do security analysis and evaluate your codes in different frameworks such as Java, .Net , PHP, Android , IOS , C++, C and more Web Apps, Desktop Apps [ Windows/ Linux/MAC], Mobile Apps [ IOS/ Android
Network Defense

Our expert team of network administrators who are skilled in protecting, detecting and responding to the threats on the network, Analyze network components, traffic, performance and utilization, network topology, location of each system, security policy to understand how networks operate
Some Tools Suites
The following are some tools we use to test and automate our hacking and penetration test process Air0 Thunder Suite
Air0 Thunder Suite
 Metasploit
Metasploit
 BackBox
BackBox
 Parrot Security OS
Parrot Security OS
 BlackArch
BlackArch
 Bugtraq
Bugtraq
 DEFT Linux
DEFT Linux
 Samurai Web Testing Framework
Samurai Web Testing Framework
 Pentoo Linux
Pentoo Linux
 Caine
Caine
 Network Security Toolkit
Network Security Toolkit
 Fedora Security Spin
Fedora Security Spin
 ArchStrike
ArchStrike
 WIFI-SLAX
WIFI-SLAX
 Wifislax
Wifislax
 Nist Cyber Framework
Nist Cyber Framework
Some Software Tools
 SQL map
SQL map Burp Suite
Burp Suite IronWASP
IronWASP Savvius
Savvius Air Crack NG
Air Crack NG Rainbow Crack
Rainbow Crack WebInspect
WebInspect L0phtCrack
L0phtCrack Medusa
Medusa IKECrack
IKECrackHardware
We keep our lab equipped with all hardware tools to start our job instant. Some of our hardware tools are.
 UberTooth One
UberTooth One
 Alfa AWUS036NHA USB WiFi Adapter
Alfa AWUS036NHA USB WiFi Adapter
 Raspberry Pi
Raspberry Pi
 Arduino MKR1000
Arduino MKR1000
 Attify Badge
Attify Badge
 Key Grabber
Key Grabber
 HackRF One Bundle
HackRF One Bundle
 LAN Tap Pro
LAN Tap Pro
 RTL-SDR
RTL-SDR
 Keysy LF RFID Duplicator and Emulator
Keysy LF RFID Duplicator and Emulator
Exploit Database
We Keep our on exploit database as our proprietary datastore . Also we always update our sources and keep an eye on open exploit data sources like below
Certification
Note : % shows how many number of people in our team have these certifications [ Professionals from 12 Countries works 24*7 with us ]
More Skills
Cyber Security Services Pricing and Plans
50k plus customers trusted with our expertise.
- Web and Cloud Security Audit
- Security audit 1 Website
- Security audit 2 Mobile Apps
- Code Review on security aspect
- Security audit 1 database
- Security audit 1 Server
- Detailed report
- Solutions guide lines for issues
- Web and Cloud Security Audit
- Security audit 1 Website
- Security audit 1 Database
- Security audit 2 Mobile Apps
- Security Audit Server / Cloud
- Detailed report
- Solutions guide lines for issues
- Code Review on security aspect
- Every 3 month We run an analysis for 1 year
- Mail us sales@airzerosec.com
- Tell us your requirement and we will tell you the cost basis of your need
- Suitable for large Enterprice Finance institution to do advanced security management.
- We will discuss with you and we can make an agreement
- Our cyber security experts are experienced and worked for many top places previously including US military , Government Security wings , and top service provider like Google, Amazon , Microsoft, Facebook etc.
- We do risk assessment (based on NIST RMF or ISO 27001 methodologies)
- Also we provide consultation for security certification with Compliance frameworks (ISO 27001, SOC 2 TSC, NIST CSF , GDPR, NIST 800-53, ISF SoGP, SANS, HIPPA, HITECH)
Mail us sales@airzerosec.com to get a custom quote